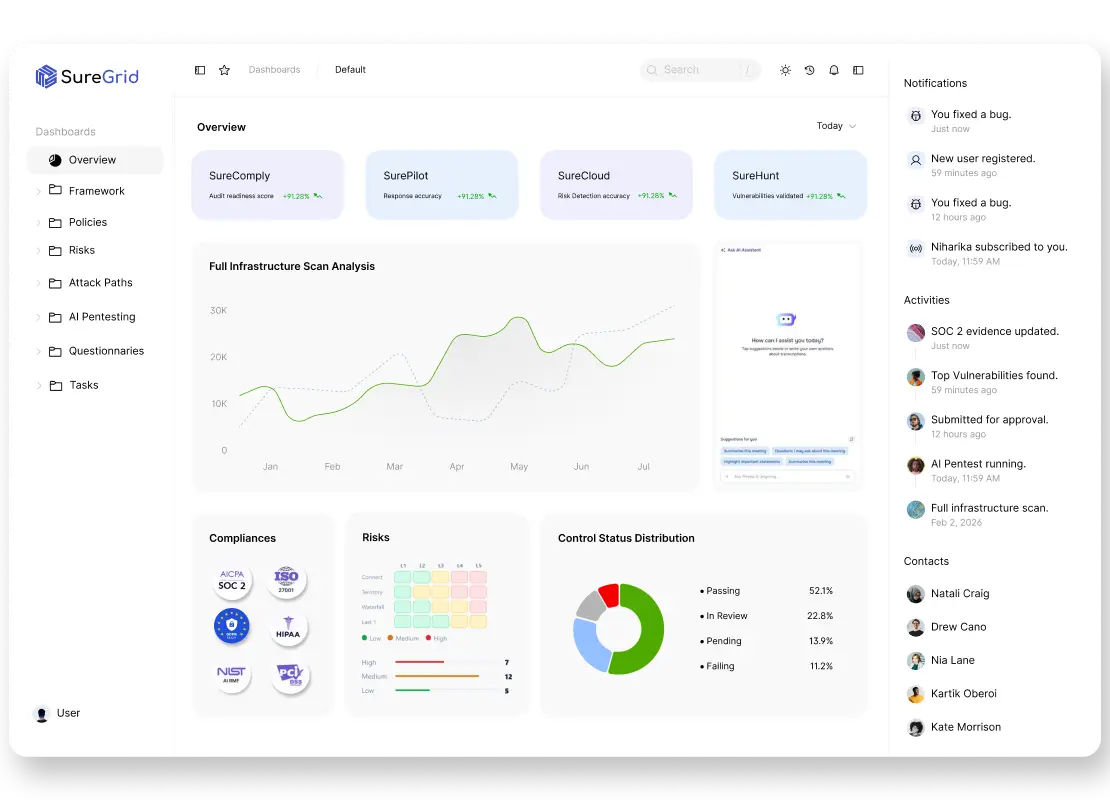
Continuous pentesting, on autopilot
Stop relying on outdated, point-in-time penetration tests. SureHunt continuously tests your applications like a real attacker — and shows what can actually be exploited right now.

Why annual pentesting is not enough
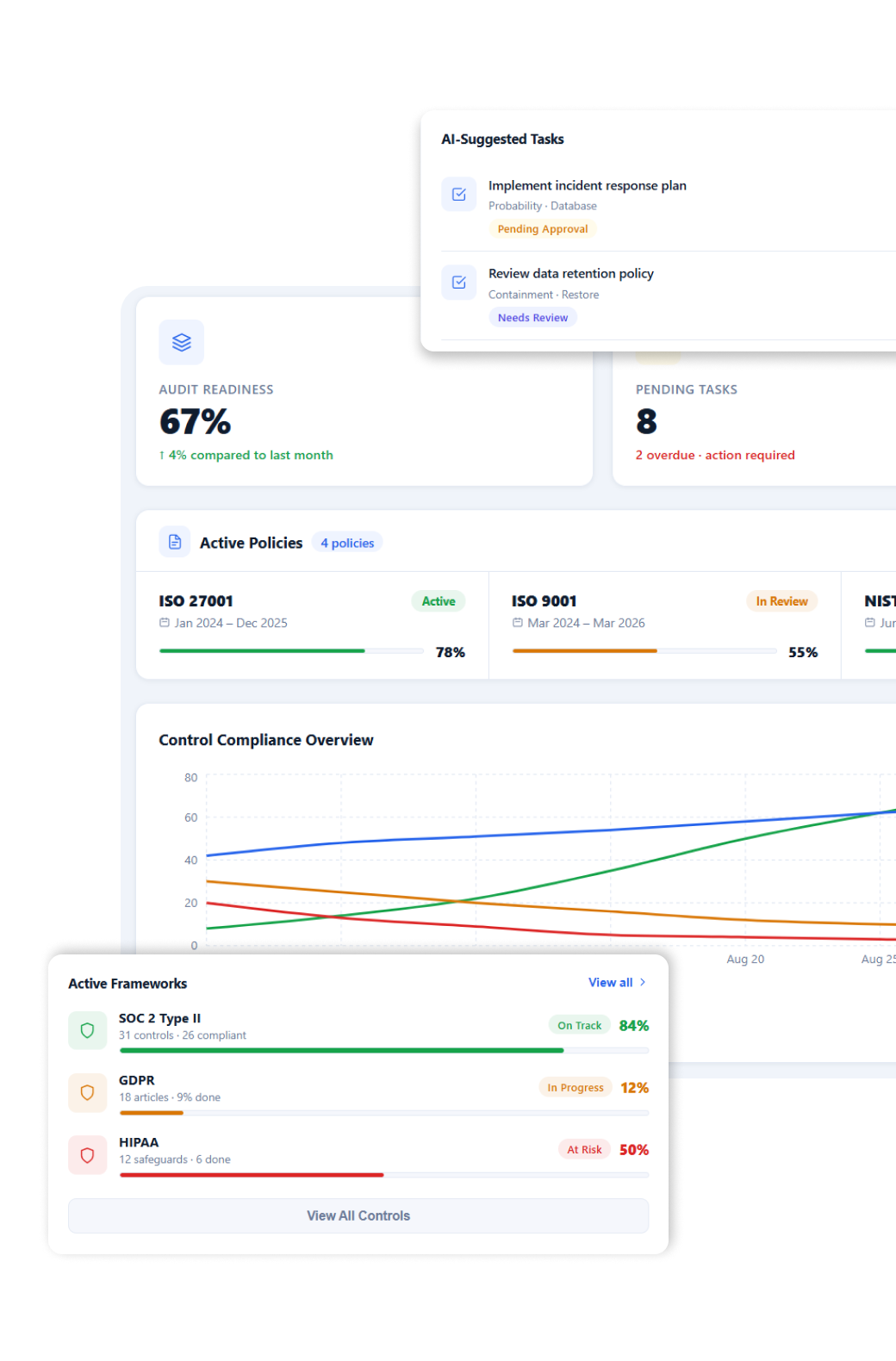
Continuous attack simulation, not static reports
Autonomous agents simulate real attacker behavior
SureHunt uses autonomous AI agents to simulate real attacker behavior across your applications and APIs, continuously probing for weaknesses the way a real adversary would. Instead of relying on predefined checks, it dynamically adapts its testing approach, uncovering complex vulnerabilities and attack paths that traditional tools often miss.
Applications, APIs, and auth flows are tested continuously
SureHunt continuously tests your applications, APIs, and authentication flows to uncover vulnerabilities across the entire attack surface. It identifies issues in real time, including logic flaws and access control weaknesses, ensuring your systems are constantly validated as they evolve with new deployments and changes.
Vulnerabilities are validated in real-world context
SureHunt validates vulnerabilities in real-world attack scenarios, ensuring every finding is tested for actual exploitability. Instead of surfacing theoretical risks, it confirms whether issues can be chained, escalated, or used to reach sensitive systems and data. This eliminates false positives and gives teams high-confidence, actionable insights on what truly needs to be fixed first.
Key Benefits
Continuous Testing Coverage
Move from annual testing to always-on validation across your applications and APIs.
Validated Exploitability
Every finding includes proof-of-exploit — no false positives or theoretical risks.
Attack Path Visibility
Understand how vulnerabilities connect into real breach scenarios, not isolated issues.
CI/CD Integration
Trigger pentests automatically on deployments and catch regressions early.
Faster Remediation
Developers get clear, actionable findings with exact steps to reproduce and fix.
Compliance-Ready Output
Meet pentesting requirements for SOC 2, ISO 27001, and other frameworks automatically.