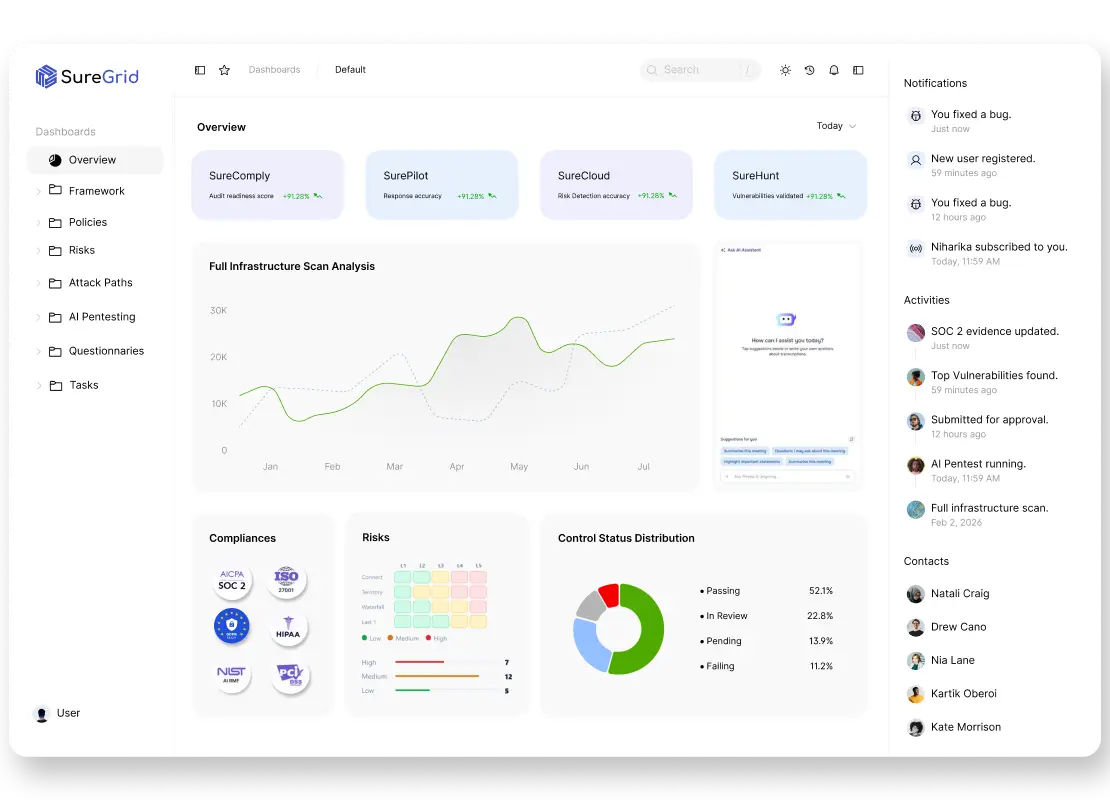
Cloud security posture management without the noise
Most CSPM tools flood you with alerts. SureCloud shows what is actually exploitable right now — and what you should fix first. Get real-time visibility across infrastructure, identities, and data, all in one place.

Alerts tell you what’s wrong, not what matters.
Focus only on risks that can actually be exploited.
Exploitability-first risk detection
SureCloud doesn’t just flag issues — it evaluates whether they can actually be used in an attack.
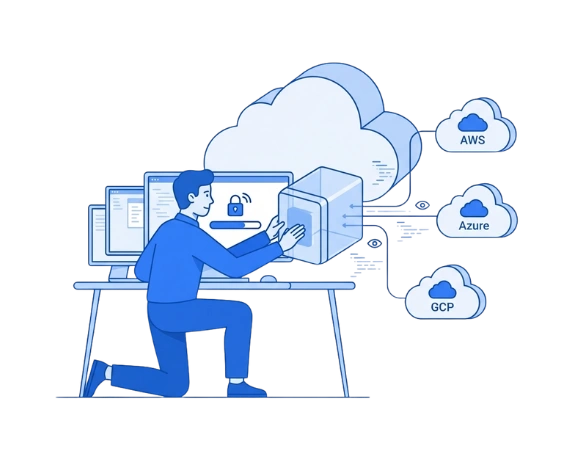
Connected cloud visibility
Infrastructure, IAM, network, vulnerabilities, and data are analyzed as one system — not in isolation.
Real-time risk awareness
Changes in your cloud are tracked instantly, so new risks are detected within minutes, not hours.
Cloud visibility that scales with you
Security Checks
0 +
Scan-to-Alert Time
0 min
Accuracy Rate
0 %
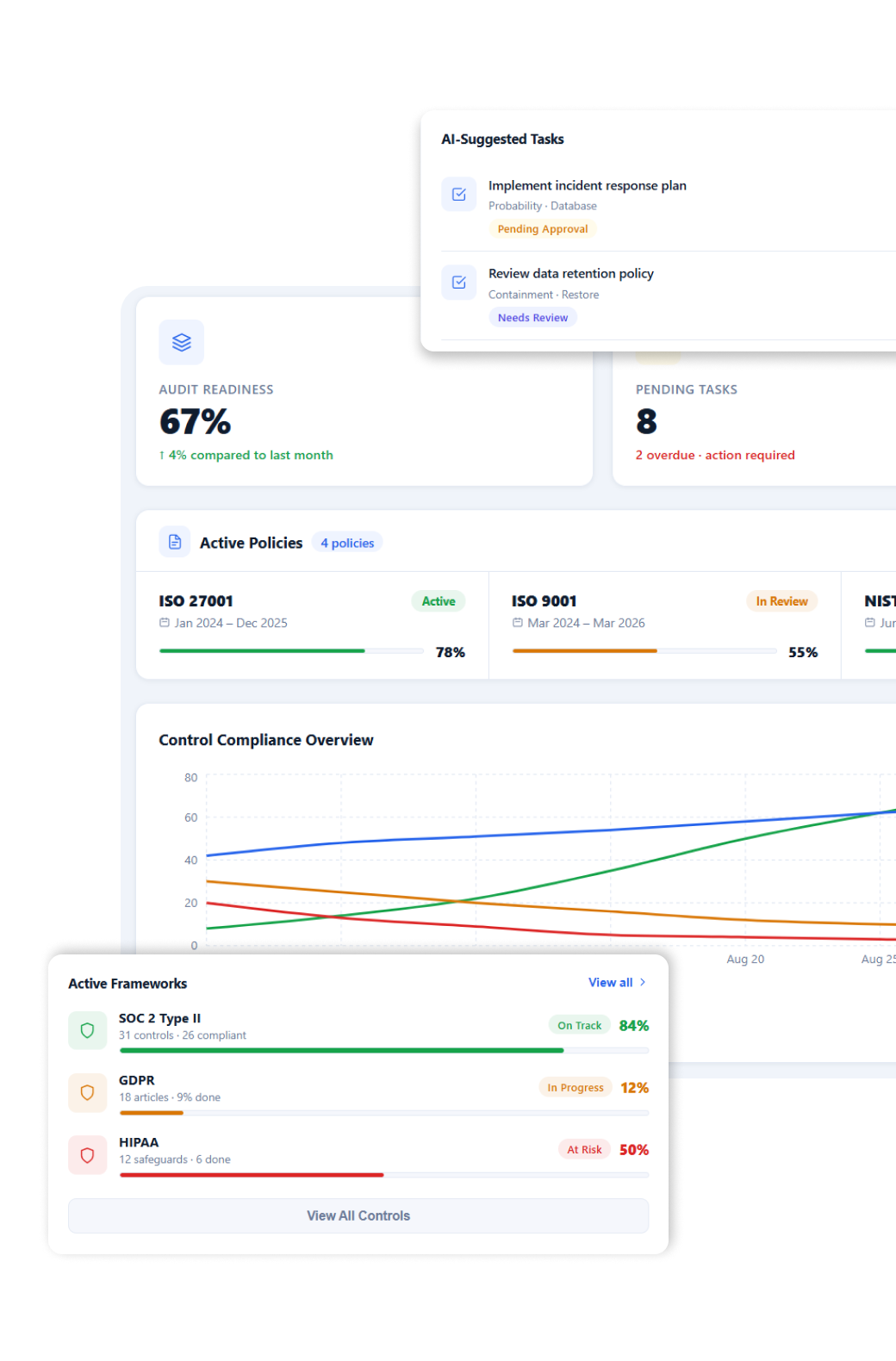
See everything. Fix what matters.
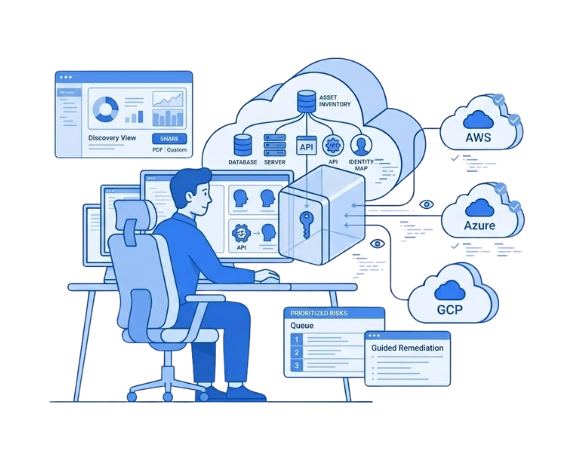
Real-Time Cloud Graph
Continuously map assets, identities, permissions, and network paths to understand how risks are connected.
Continuous Asset & Identity Inventory
Maintain a live inventory of all cloud resources, users, roles, and environments across AWS, Azure, and GCP.
Exploitability-Based Prioritization
Prioritize risks based on real attack potential — not just severity labels.
Compliance-Aware Risk Mapping
Link cloud risks directly to compliance frameworks like SOC 2, ISO 27001, and CIS.
Context-Aware Remediation
Get clear, environment-specific guidance with scripts, steps, and safe execution options.
DevSecOps & CI/CD Integration
Push findings into developer workflows, block risky changes, and align security with deployment speed.
How SureCloud Works
Step – 1 Connect your cloud
Start by linking
SureCloud quickly discovers your cloud resources, identities, and configurations to build a complete, live inventory without making any changes to your environment.
Step 2 – Map your environment
SureCloud maps your entire environment
SureCloud connects everything into one structured graph, showing what exists, how systems are connected, and who owns them, creating full visibility from day one.
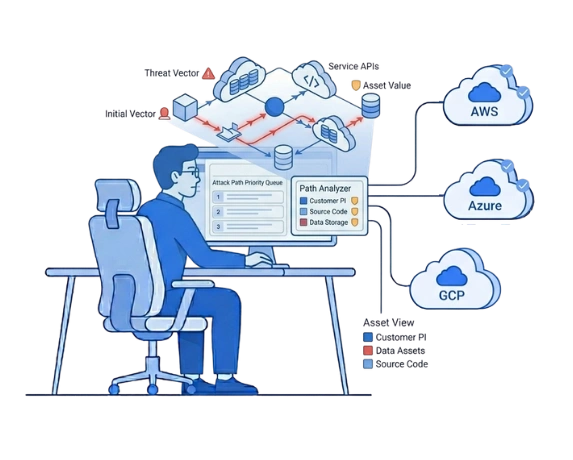
Step 3 – Monitor and detect risk continuously
SureCloud continuously monitors
SureCloud continuously monitors configurations, access, and deployments, correlating exposure, permissions, vulnerabilities, and data sensitivity to detect what actually matters.

Step 4 – Understand attack paths and prioritize
SureCloud connects exposure
Instead of isolated alerts, SureCloud maps real attack paths, showing how an attacker could move through your environment, and prioritizes only the most critical, exploitable risks.
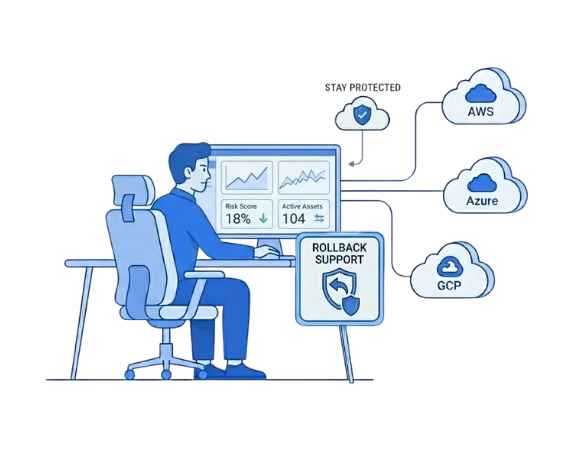
Step 5 – Fix and stay protected
SureCloud maps how an attacker could move across your cloud
With guided remediation, approvals, and automation, teams can fix issues confidently. SureCloud continues monitoring to ensure risks do not reappear as your environment evolves.
What Our Clients Say