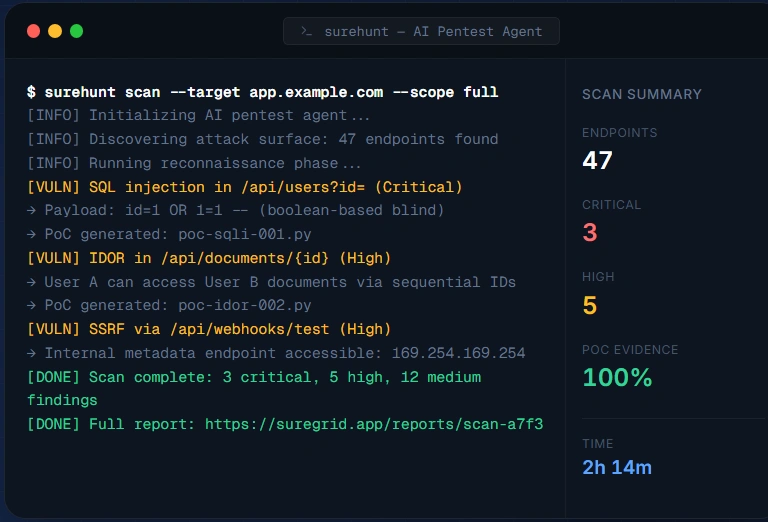
AI Penetration Testing Proof, not promises.
Traditional pentests tell you what might be wrong. SureHunt shows what can actually be exploited right now. Continuously simulate real attacker behavior, validate exploit paths, and get clear, prioritized fixes — not reports.
You only test security occasionally
Continuously validate real-world attack paths.
Continuous Environment Coverage
Stay protected as your system evolves. SureHunt adapts to deployments, configuration changes, and new exposures, ensuring your attack surface is always up to date.
Noise Reduction by Design
Focus only on what truly matters. SureHunt filters out non-impactful findings and highlights only risks that contribute to real security exposure.
End-to-End Risk Visibility
Understand the full impact of a breach. See how issues affect critical systems, data, and business operations—not just where they exist.
See how attackers think. Fix what actually matters.
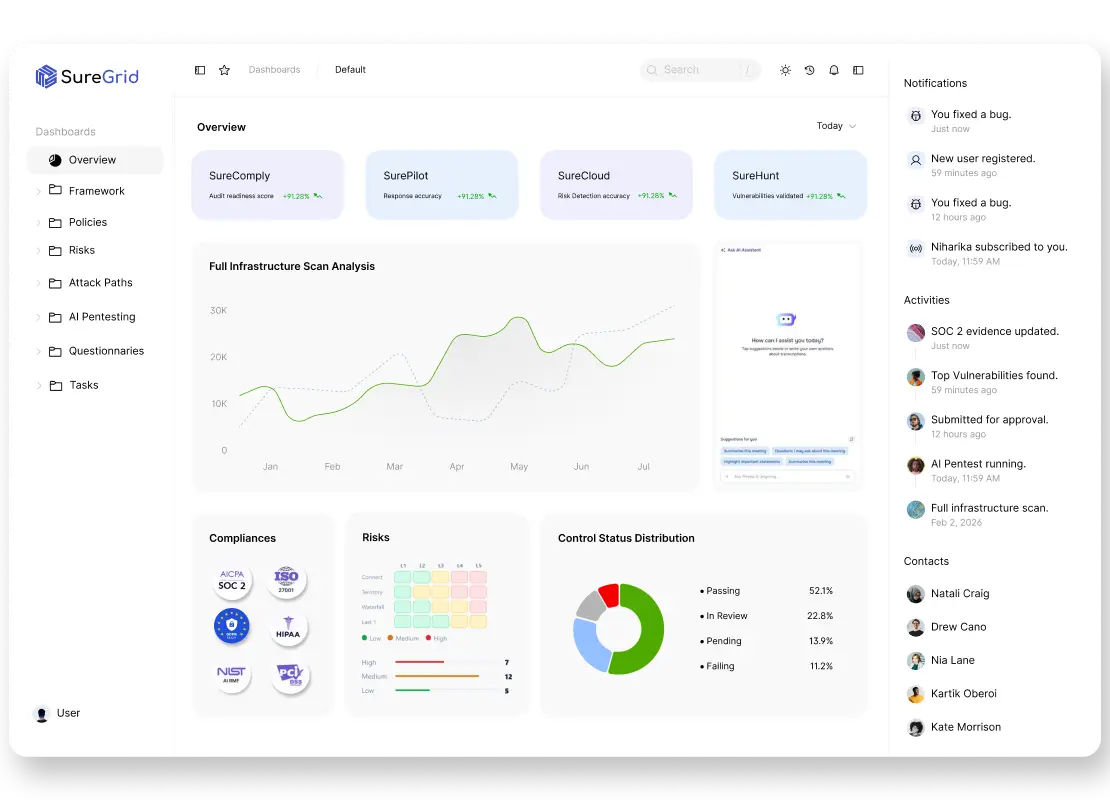
Continuous AI Pentesting
Autonomous agents continuously simulate real-world attacks across applications and APIs.
Dynamic Attack Surface Discovery
Automatically discover APIs, endpoints, subdomains, and hidden attack surfaces.
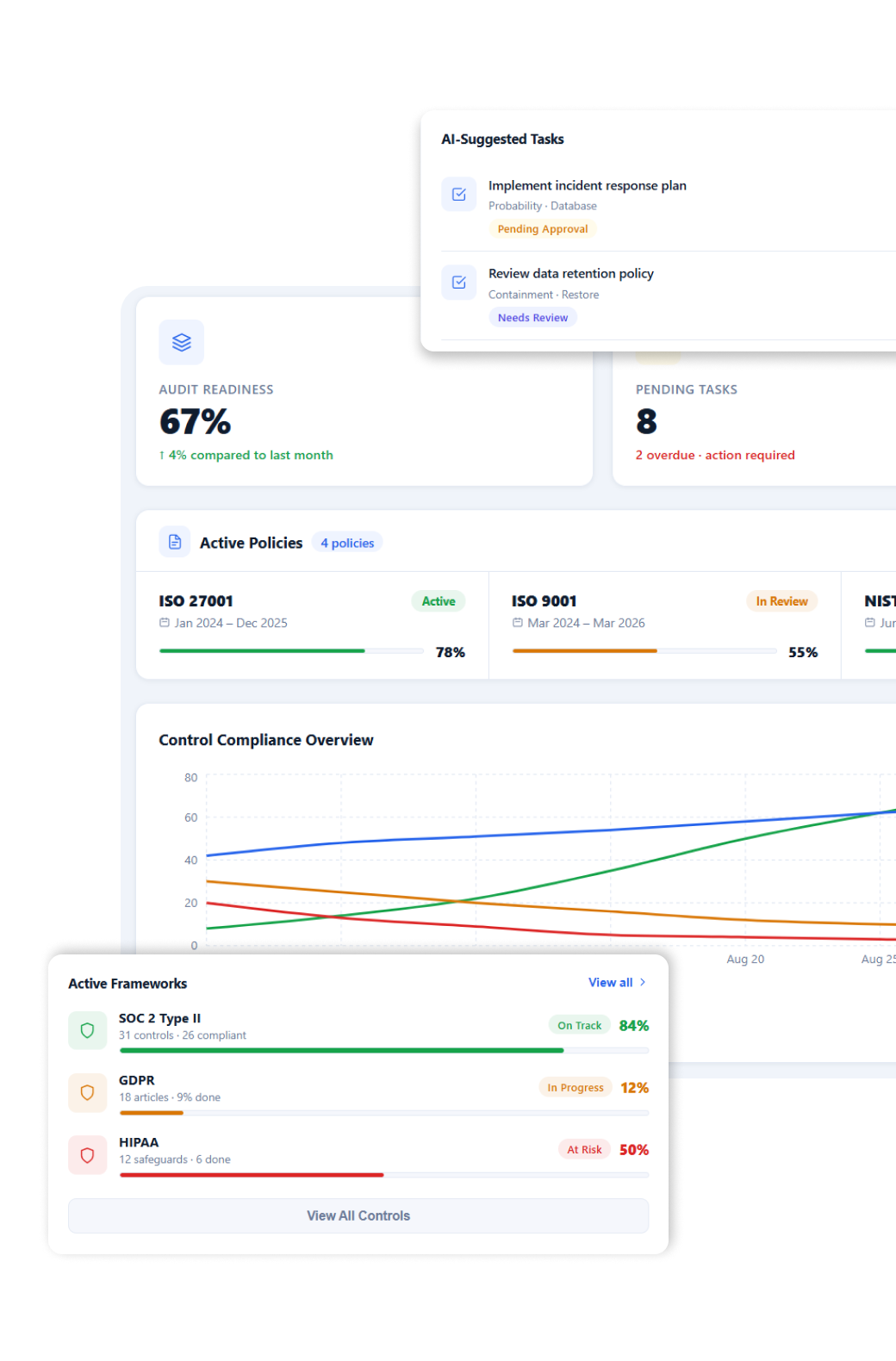
Validated Attack Graphs
Visualize how vulnerabilities chain together into real attack paths.
Safe Proof-of-Exploit Validation
Every finding includes non-destructive proof — validated safely in production or staging.
Risk-Based Prioritization
Get a single queue of what actually matters, based on exploitability and impact.
CI/CD & Workflow Integration
Trigger pentests on deploy and push findings directly into engineering workflows.
From attack simulation to continuous protection
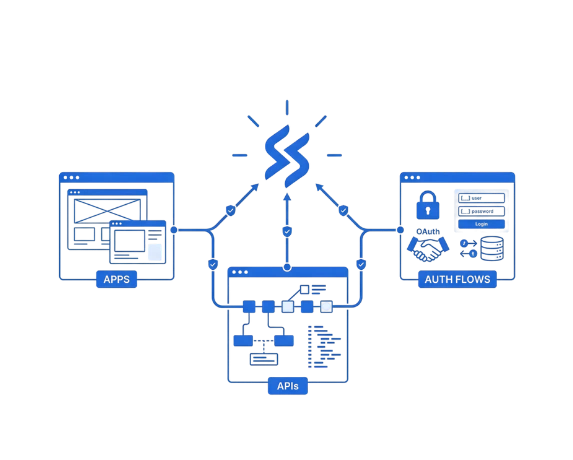
Step 1 – Connect your applications
Connect your applications, APIs, and authentication flows securely
SureHunt connects to your web applications, API specifications, and authentication methods to understand how your system is accessed. This builds a complete view of your attack surface from the start.
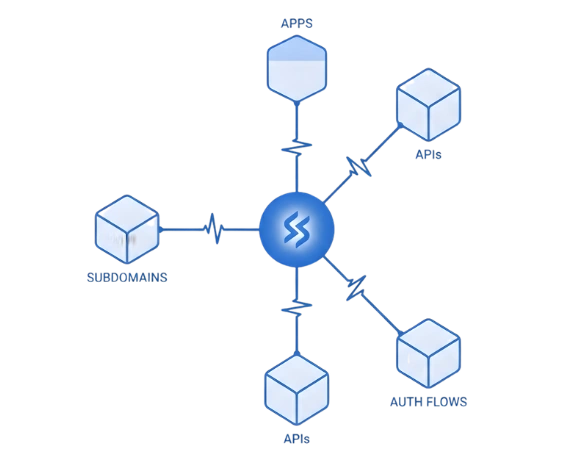
Step 2 – Discover your attack surface
SureHunt continuously discovers and maps your entire attack
SureHunt continuously maps your environment like a real attacker, uncovering exposed and hidden entry points so you know exactly where attacks can begin.
Step 3 – Run continuous pentests
SureHunt runs continuous
AI agents continuously test your applications across deployments, configuration changes, and new exposures, ensuring security is always up to date.
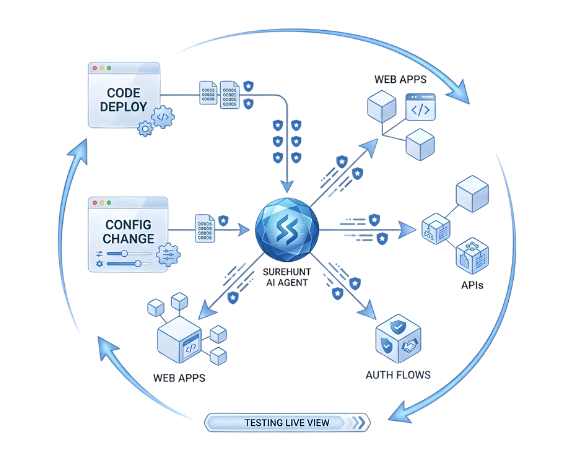
Step 4 – Identify and prioritize real risks
SureHunt identifies real weaknesses
SureHunt connects weaknesses into real attack paths and validates exploitability, prioritizing only the risks that can actually lead to a breach.

Step 5 – Fix, validate, and stay protected
SureHunt connects individual weaknesses into multi-step attack paths
With guided remediation and automatic re-testing, SureHunt confirms that risks are fully resolved and continuously monitors for regressions as your system evolves.