NIST 800-171 is a compliance mandate for every business and contractor that works with U.S government data and needs to access and store sensitive federal data that is not categorised as “classified”. In this blog, we will break down what NIST SP 800-171 is, why it matters, and how you can achieve compliance without getting lost in the technical weeds.
What is NIST SP 800-171?
NIST SP 800-171 is a set of security standards created by the National Institute of Standards and Technology. Its full title is “Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations.”
In simple terms, the U.S government wants to make sure that when they share sensitive information that is not considered classified with private companies, those companies have a strong “digital lock” to prevent any data leak.
Why it matters today
Cyberattacks on the defense supply chain are at an all-time high. Smaller contractors are often seen as “weak links” by hackers. NIST 800-171 was designed to strengthen these links and protect national security.
Who needs to comply?
If you are a contractor or subcontractor for the DoD, General Services Administration (GSA), or NASA, you likely need to comply. If your contract includes the DFARS clause 252.204-7012, NIST SP 800-171 compliance is a legal requirement.
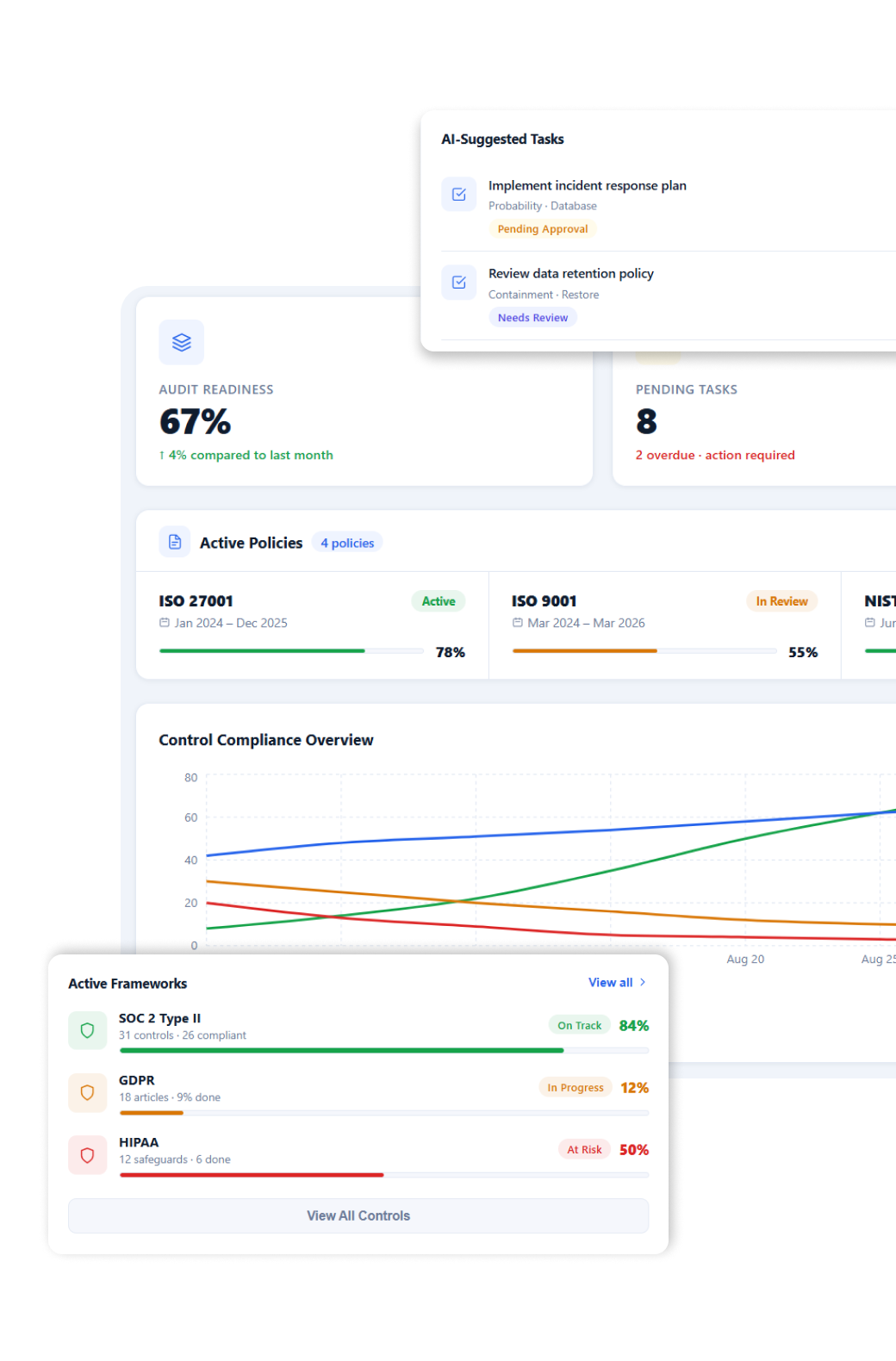
Simplify Your Compliance & Stay Audit-Ready
Help your team manage controls, risks, and audits with ease
What is Controlled Unclassified Information (CUI)?
To understand the rules, you first need to understand what you are protecting. This is called Controlled Unclassified Information (CUI).
CUI is information that isn’t classified as “Secret” or “Top Secret,” but still requires protection because it is sensitive to national interests.
Examples of CUI include:
- Engineering drawings: Blueprints for a military vehicle part.
- Research data: Studies on new materials for aircraft.
- Technical specifications: Manuals for communication equipment.
- Legal documents: Details about government contracts or proprietary processes.
Think of CUI as the “secret sauce” of government projects. Even if it isn’t a state secret, if a foreign adversary gets a hold of it, they could copy our technology or find weaknesses in our systems.
Overview of NIST SP 800-171
The primary purpose of NIST SP 800-171 is to protect CUI residents in “nonfederal” systems meaning the computers and servers owned by private companies like yours.
The Framework Structure
The framework is not just a random list of tips. It consists of 110 security requirements grouped into 14 “Families.”
These requirements focus on technical security (like passwords) and physical security (like locking the server room door).
The 14 Control Families Explained
On paper the 110 requirements may seem like a big daunting list. But to simplify these requirements they can be divided in 14 categories which are called as Control Families:
- Access Control: Who can see your data? (Limiting system access to authorized users).
- Awareness and Training: Do your employees know not to click on suspicious links?
- Audit and Accountability: Can you track who did what in your system and when?
- Configuration Management: How are your systems built and updated?
- Identification and Authentication: How do users prove who they are? (e.g., Multi-Factor Authentication).
- Incident Response: What is your “fire drill” if you get hacked?
- Maintenance: How do you keep your machines running safely?
- Media Protection: How do you protect USB drives, hard drives, and paper records?
- Personnel Security: Are your employees screened before they access CUI?
- Physical Protection: Are your offices and server rooms locked?
- Risk Assessment: Do you regularly check for “holes” in your security?
- Security Assessment: Are your security plans actually working?
- System and Communications Protection: How is data protected while it’s being sent? (Encryption).
- System and Information Integrity: How do you spot and fix system errors or malware?
NIST SP 800-171 and CMMC Level 2
If you follow defense news, you’ve heard of the Cybersecurity Maturity Model Certification (CMMC). You might be wondering: “Do I need NIST 800-171 or CMMC?”
The answer is both.
CMMC Level 2 compliance standards are directly mapped to the 110 controls of NIST SP 800-171. Essentially, NIST is the test and CMMC is the certification.
- The Content: CMMC Level 2 requirements are identical to the NIST SP 800-171 requirements.
- The Difference: NIST 800-171 historically allowed for “self-assessment.” CMMC Level 2 will eventually require a third-party audit (C3PAO) for most contractors to verify that you are actually doing what you say you are doing.
The NIST SP 800-171 DoD Assessment Methodology
The DoD doesn’t just take your word for it anymore. They use a specific NIST SP 800-171 DOD assessment methodology to score your compliance.
How Scoring Works
The highest possible score is 110. You start at 110 and lose points for every control you haven’t fully implemented. Some points are “heavier” than others. Failing a major control could cost you 5 points, while a minor one might cost 1 point.
The Role of SPRS
Once you complete a self-assessment, you must upload your score to the Supplier Performance Risk System (SPRS). The DoD checks this database before awarding contracts. If your score is low or missing, you might be disqualified from bidding.
Key Compliance Requirements
While all 110 controls matter, there are a few “heavy hitters” that form the foundation of your security:
- System Security Plan (SSP): This is a living document that describes how you meet every single one of the 110 controls. It is the “map” of your security.
- Plan of Action and Milestones (POA&M): If you aren’t meeting a requirement yet, the POA&M is your “to-do list” explaining how and when you will fix it.
- Access Control: Implementing Multi-Factor Authentication (MFA) is one of the most effective ways to stop 90% of attacks.
- Incident Response: You must have a written plan for how to report a breach to the DoD within 72 hours.
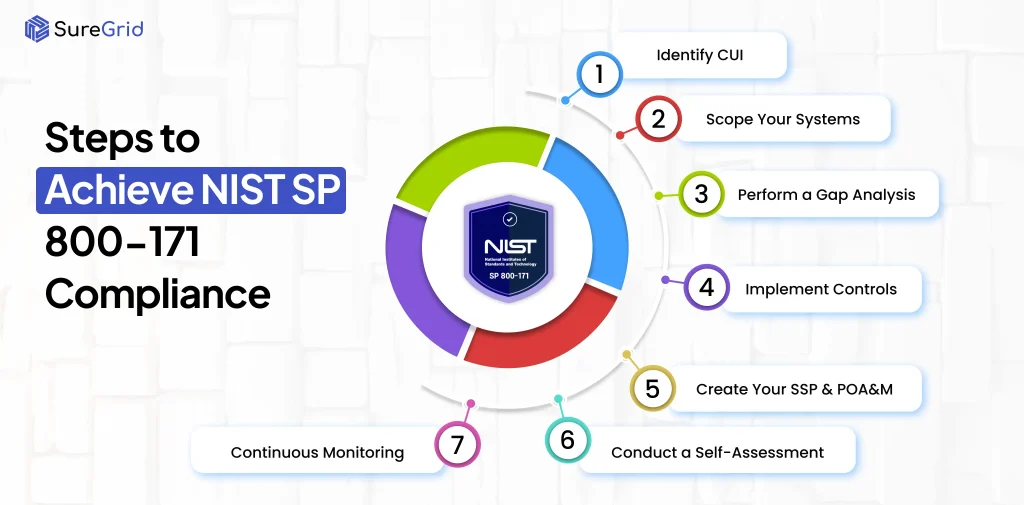
Step-by-Step Guide to Achieving Compliance
Ready to get compliant? Follow these seven steps:
Step 1: Identify CUI
Talk to your contracting officer. Ask exactly which data is considered CUI. You can’t protect it if you don’t know where it is.
Step 2: Scope Your Systems
Do you need to protect your whole company or just one specific server? “Scoping” means deciding which parts of your network touch CUI. Narrowing your scope can save you thousands of dollars.
Step 3: Perform a Gap Analysis
Compare your current security to the 110 NIST controls. Where are the “gaps”? This is usually done by an IT professional or an automated tool.
Step 4: Implement Controls
This is the “doing” phase. Set up the encryption, buy the locks, and write the policies needed to close the gaps found in Step 3.
Step 5: Create Your SSP & POA&M
Document everything. If it isn’t written down in your System Security Plan, the DoD considers it non-existent.
Step 6: Conduct a Self-Assessment
Score yourself using the DoD Assessment Methodology. Be honest! If you have gaps, put them in your POA&M.
Step 7: Continuous Monitoring
Compliance is not a “one and done” task. You must regularly check your logs, update your software, and retrain your staff.
Common Challenges and Mistakes
Many companies fail their audits because of these common errors:
- Over-scoping: Trying to make your entire office compliant when only two people handle CUI. This makes compliance much more expensive than it needs to be.
- Poor Documentation: Having a great firewall but no written policy explaining who manages it.
- The “One-Time Effort” Mindset: Thinking that once you upload your score to SPRS, you are finished. Security must be managed every day.
- Lack of Visibility: Not knowing what devices are connected to your network. You can’t protect what you can’t see.
Best Practices for Faster Compliance
- Use Automation: There are tools that can scan your network and automatically tell you which NIST controls you are missing.
- Employee Training: Your staff is your first line of defense. A simple 15-minute monthly training session can prevent a multi-million dollar breach.
- Keep it Simple: Don’t buy the most expensive security software if a simple configuration change in Windows or Microsoft 365 can do the same thing.

Benefits of NIST SP 800-171 Compliance
Aside from not getting sued or losing your contracts, there are major business benefits:
- Better Security: You are significantly less likely to suffer from ransomware or data theft.
- Contract Eligibility: You can bid on high-value DoD and federal contracts that your competitors can’t.
- Trust: Large prime contractors (like Lockheed Martin or Boeing) prefer working with subcontractors who prove they take security seriously.
- CMMC Readiness: Since CMMC Level 2 is based on NIST 800-171, you are already 95% of the way to being CMMC certified.
Conclusion
NIST SP 800-171 compliance is essential for protecting your business and the future of the defense supply chain. By thoroughly learning all 14 control families, scoping your systems correctly, and creating and maintaining a Parameter (SSP) System Security Plan, you will do more than meet a legal requirement. You will be at CMMC Level 2 and will have demonstrated to the DoD that your business is trustworthy. Although the 110 controls may initially seem intimidating, an active approach with continuous monitoring and documentation will help your security requirements from becoming an obstacle to becoming a strategic advantage.
FAQs
Ques: What is NIST 800-171?
Ans: NIST 800-171 is a security framework that helps businesses in protecting sensitive government data called CUI when it is stored or processed outside of US government systems.
Ques: Who needs to comply with NIST SP 800-171?
Ans: Any business that is working with the U.S Government especially with DoD, GSA, or NASA must be compliant with NIST SP 800-171.
Ques: How many requirements are there in NIST 800-171?
Ans: NIST SP 800-171 has 110 requirements which are categorized under 14 categories.
Ques: What is the difference between NIST SP 800-171 and CMMC Level 2?
Ans: NIST SP 800-171 provides the security controls, while CMMC Level 2 is the certification framework that verifies whether those controls are properly implemented.
Ques: How is NIST 800-171 compliance scored?
Ans: The DoD assessment starts with a score of 110. Points are deducted for each unmet control, and the final score is submitted to the SPRS system.
Ques: What is CUI?
Ans: CUI stands for Controlled Unclassified Information and it refers to sensitive information that needs to be protected but not categorised as “Classified”.