Companies manage a huge amount of operational and customer data using cloud-based platforms SaaS software, as well as remote servers. Cyber-attacks are growing, and organizations have to prove that they are able to manage sensitive data and keep it safe. Data breaches are on the rise each year. SOC 2 Certification helps organizations build secure systems, decrease security risks, and create confidence.
What is SOC 2 Certification?
SOC 2 certification is a conformity attestation. The AICPA auditors award this certification. It proves that companies have established effective security measures to safeguard customers’ data. This framework of compliance reviews the practices of an organization against the five Trust Service Criteria, which include availability, security, confidentiality, integrity of processing, and privacy. It is widely accepted by SaaS, cloud, and technology companies to show high levels of operational and data security.
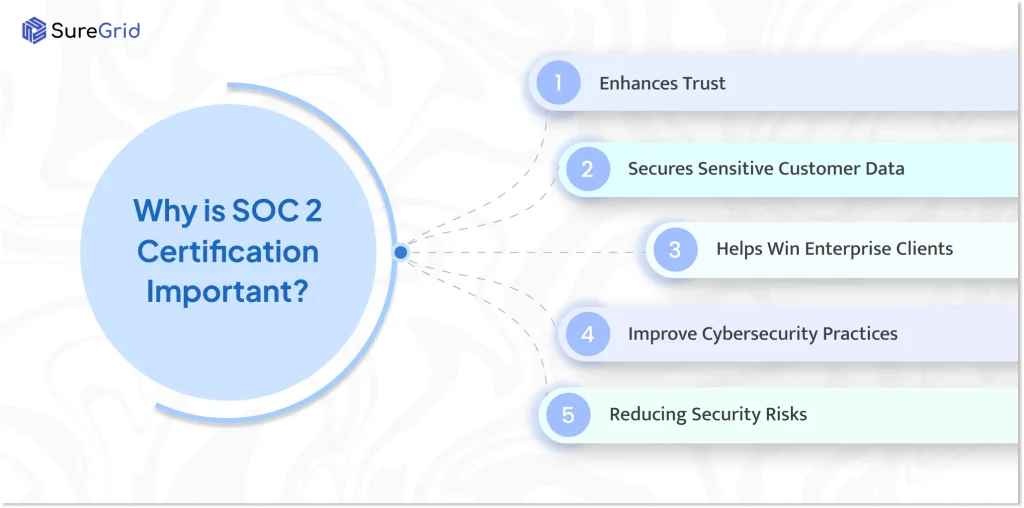
Why is SOC 2 Certification Important?
This certification is essential for a business for the reasons listed below:
- Enhances Trust: It reassures customers, stakeholders, and partners that the company adheres to strict security procedures and safeguards sensitive data.
- Secures sensitive customer data: Helps organizations establish security measures to avoid leaks, breaches, or unauthorised access to sensitive information.
- Helps Win Enterprise Clients: Many of the largest firms’ clients require vendors to be in SOC 2 compliance before signing agreements or sharing sensitive information.
- Improve Cybersecurity practices: The process of certification is a way for businesses to ensure that access controls are secure, to use encryption, monitoring, and also risk management.
- Reducing Security Risks. Regular security audits and checks can help detect weaknesses before they turn into significant problems
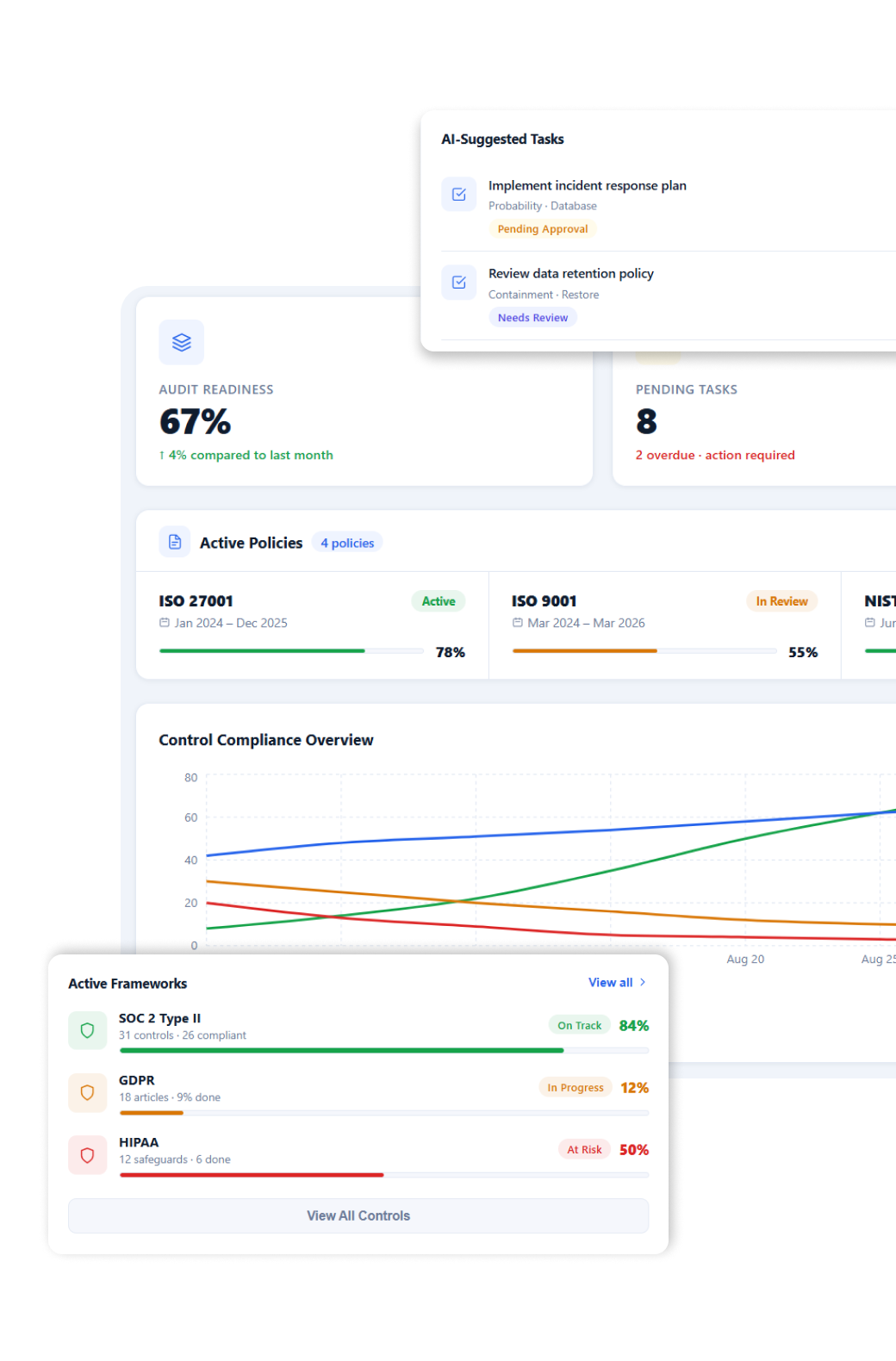
Simplify Your Compliance & Stay Audit-Ready
Help your team manage controls, risks, and audits with ease
Type of SOC 2 Reports
There are mainly two types of SOC 2 Reports based on the scope and duration of the audit process:
SOC 2 Type 1 Certification
A SOC 2 Type 1 report checks whether an organization’s security controls are designed at a specific point in time. It checks if a company has implemented the necessary systems, policies, and procedures to protect customer information.
Key Features:
- Point-in-time assessment.
- Reviews the design of security controls.
- Faster and less expensive than Type II
- Suitable for startup and early-stage companies
- Demonstrates initial compliance readiness
SOC 2 Type 2 Certification
A SOC 2 Type 2 report checks both the design and operational effectiveness of security controls over a defined monitoring period, usually between 3 and 12 months. It provides deeper assurance that the organization consistently follows its security practices.
Key Features
- Assess controls over a period of time
- Tests operational effectiveness
- Preferred by enterprise customers and investors
- More detailed and comprehensive audit
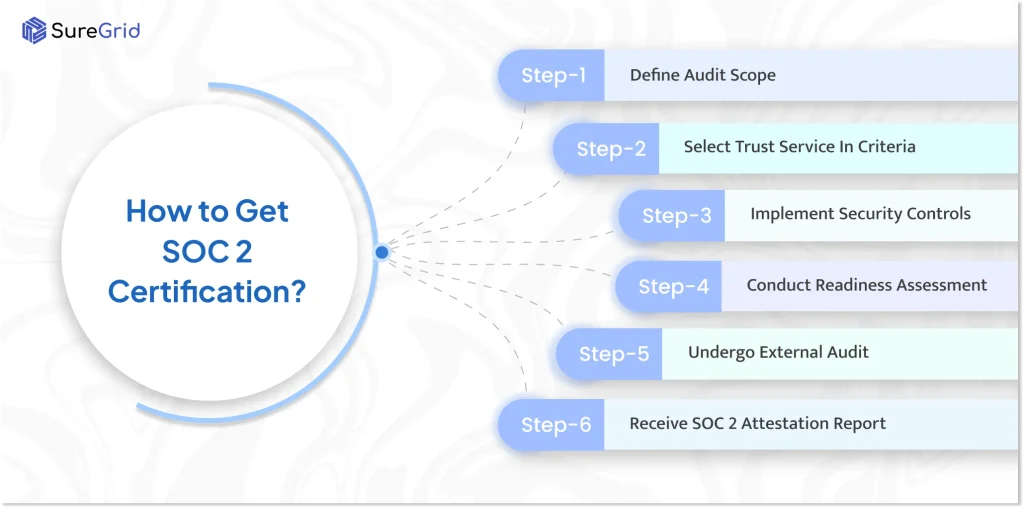
How to Get SOC 2 Certification?
Step 1: Define Audit Scope
It is the process of determining the scope of the audit. The business must identify which systems, applications, infrastructure, vendors, and internal processes will be included in the assessment.
It involves:
- Business units covered under the unit
- Customer data and sensitive information are handled
- Cloud platforms and third-party services are used
- Employees and departments involved in security operations
Step 2: Select Trust Service in Criteria
The SOC 2 audit is based on the Trust Services Criteria (TCS). Each SOC 2 audit includes the security criterion, while additional criteria depend on the business operations and customer requirements.
The five Trust Service Criteria are:
- Security
- Availability
- Confidentiality
- Processing Integrity
- Privacy
Step 3: Implement Security Controls
After selecting the Trust Service Criteria, the business must implement technical, administrative, and operational controls to meet SOC 2 requirements.
Common SOC 2 security controls include:
- Multi-Factor Authentication (MFA)
- Access Control Management
- Endpoint Security
- Data Encryption
- Employee security awareness training
- Incident Response Planning
- Vendor risk management
- Backup and disaster recovery processes
The organization must also create formal policies and maintain evidence showing that these controls are enforced.
Step 4: Conduct Readiness Assessment
Many companies perform a readiness assessment or gap analysis. The internal review helps find missing controls, policy gaps, and compliance weaknesses that could impact audit results.
A readiness assessment typically includes:
- Reviewing security documentation
- Evaluating existing controls
- Testing monitoring systems
- Identifying compliance gaps
- Preparing audit evidence
Organizations reduce audit risks and improve overall preparedness before engaging an external auditor.
Step 5: Undergo External Audit
The CPA firm conducts the official SOC 2 audit or an accredited auditing organization. During an audit, the auditor evaluates whether the implemented controls satisfy SOC 2 requirements:
SOC 2 Type I, the auditor assesses whether controls are properly designed at a specific point in time.
SOC 2 Type II, the auditor checks how effectively the control operates over a monitoring period, usually between 3 to 12 months.
In this process, the auditor reviews:
- Security Policies
- Access Logs
- Monitoring Records
- Incident Management Procedures
- Employee Training Evidence
- Vendor Management Practices
Audit duration depends on the company size, infrastructure complexity, and the selected Trust Service Criteria.
Step 6: Receive SOC 2 Attestation Report
After completing the audit, the auditing firm issues a SOC 2 attestation report detailing;
- Audit Scope
- Systems Reviewed
- Applicable Trust Service Criteria
- Auditor Findings
- Control Effectiveness
- Exceptions or observations, if any
What is the SOC 2 Certification Cost?
For startups and small businesses, SOC 2 certification may cost around $10,000 to $25,000. Mid-sized and larger organizations usually spend according to the infrastructure and compliance needs.
SOC 2 Type II certification is typically more expensive than Type I. Because it analyses how security controls perform over a monitoring period of several months.
What is the difference between SOC 2 Type 1 and Type 2 Certification?
There are main differences between SOC 1 Type 1 and SOC 2 Type 2:
| Basis | SOC 2 Type 1 | SOC 2 Type 2 |
| Definition | Check whether security controls are properly designed at a specific point in time. | Check whether security controls are designed and operating effectively over a period of time. |
| Focus | Design of Controls | Design and operational effectiveness of controls |
| Audit Period | Single date or snapshot | Continuous review over several months |
| Duration Covered | Point in time assessment | Usually 3 to 12 months |
| Purpose | Confirms controls | Confirms controls consistently work over time |
| Level of Assurance | Lower assurance | Higher assurance |
| Adit Complexity | Less complex and faster | More detailed and rigorous |
| Time to Obtain | Can be completed quickly | Takes longer due to the monitoring period |
| Cost | Generally Lower | Generally Higher |
| Evidence Required | Documentation and policy review | Documentation, monitoring logs, and operational evidence |
| Best For | Startups or companies beginning compliance | Mature organizations handling sensitive customer information |
| Customer Trust | Basic trust validation | Stronger trust and credibility |
What is the time required to achieve SOC 2 Certification?
Generally, achieving SOC compliance takes many months:
- SOC 2 Type 1: It generally takes about 1 to 3 months. It focuses on whether a company has the right security controls and policies in place at a specific time.
- SOC 2 Type 2: It usually takes around 6 months to 12 months. It checks whether those security controls are working properly over a longer period of time.
Conclusion
A SOC Certification is essential for businesses to prove that the organization protects customer information. Achieving this certification helps businesses close good deals because big enterprises ask for SOC 2 certification before doing any business. There are mainly two types of SOC 2 Certification SOC 1 Type 1 and SOC 2 Type 2 Certification. Above, we have mentioned the steps to achieve the SOC 2 type certification.
FAQs
Ques: What is SOC 2 Certification?
Ans: It is a compliance certification that confirms that tech companies securely handle customer information.
Ques: Is ISO 27001 the same as SOC 2?
Ans: They both focus on security standards; they are two different frameworks.
Ques: How to be ISO 2 Certified?
Ans: You need to implement SOC controls to secure, complete an audit, and pass the certification.
Ques: What is the SOC Compliance Checklist?
Ans: It is a list of security, privacy, availability, and controls requirements used to prepare for SOC audits.
Ques: What is the validity of the SOC 2 Certificate?
Ans: It is valid for 12 months; after that, the companies undergo a new audit.